Russian Intelligence Exploits EoL Routers in Massive DNS Hijacking Campaign
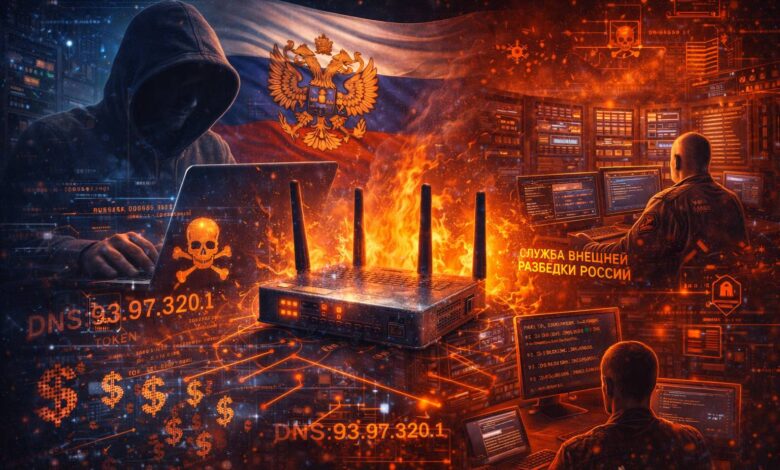
Security researchers have uncovered a large-scale espionage operation orchestrated by Russian military intelligence, leveraging aging networking hardware to bypass modern security protocols and harvest user authentication tokens.
Microsoft and Black Lotus Labs, the security arm of Lumen Technologies, issued a joint warning on Tuesday regarding a sophisticated “Adversary-in-the-Middle” (AiTM) campaign. The operation, attributed to the GRU-linked threat actor Forest Blizzard (also known as APT28 or Fancy Bear), successfully compromised over 18,000 networks globally.
Unlike traditional cyberattacks that rely on deploying sophisticated malware, Forest Blizzard utilized a “low-tech” but highly effective method: hijacking the Domain Name System (DNS) settings of end-of-life (EoL) and unpatched Small Office/Home Office (SOHO) routers. By exploiting known vulnerabilities in older MikroTik and TP-Link devices, the attackers redirected traffic to malicious servers under their control.
Bypassing Multi-Factor Authentication (MFA)
The strategic brilliance of the campaign lies in its focus on OAuth authentication tokens. When a user logs into a service like Microsoft Outlook, these tokens are generated to maintain the session, typically after the user has completed multi-factor authentication (MFA).
By sitting between the user and the service via DNS redirection, Forest Blizzard intercepted these tokens in real-time. This allowed the state-backed actors to gain direct access to victim accounts without the need for phishing credentials or intercepting one-time codes. According to Microsoft, the campaign successfully targeted more than 200 organizations and 5,000 consumer devices, with a primary focus on government agencies, law enforcement, and foreign affairs ministries.
Evolution of Tactics
The shift toward DNS hijacking represents a tactical pivot for the GRU. Following a previous disclosure by the U.K.’s National Cyber Security Centre (NCSC) in August 2025, the group reportedly abandoned malware-based router control in favor of this more systemic, “graybeard” approach.
“These guys didn’t use malware,” said Ryan English, Security Engineer at Black Lotus Labs. “They did this in a way that isn’t really sexy, but it gets the job done.”
The scale of the December 2025 peak suggests a highly automated exploitation of the SOHO market, where devices are frequently neglected and rarely updated by end-users.
Regulatory Fallout
The exposure of this vulnerability comes amid heightened regulatory scrutiny of networking hardware. On March 23, 2026, the U.S. Federal Communications Commission (FCC) announced a sweeping policy change, halting the certification of consumer-grade routers produced outside the United States unless they receive specific security clearances.
The FCC cited foreign-made routers as an “untenable national security threat,” arguing that poorly secured edge devices provide a gateway for adversaries to disrupt critical infrastructure. While the policy has faced criticism regarding market availability, the Forest Blizzard campaign underscores the technical reality that unpatched edge devices remain a primary vector for state-sponsored espionage.
The Forest Blizzard campaign highlights a critical shift in the threat landscape: the weaponization of the “Network Edge” to neutralize “Identity” security. As enterprises have moved toward Zero Trust architectures and MFA to secure the identity layer, state-sponsored actors have regressed to the infrastructure layer to intercept the byproduct of a successful login—the session token.
From a technical standpoint, this operation demonstrates that the industry’s reliance on TLS and MFA is only as strong as the underlying routing integrity. When the DNS resolution is compromised at the hardware level, the “web of trust” is effectively bypassed. We expect this to trigger a mandatory industry move toward Encrypted DNS (DNS over HTTPS/TLS) as a default setting in enterprise environments, and likely a more aggressive push by ISPs to forcibly retire EoL SOHO hardware that can no longer receive security microcode updates. This campaign serves as a definitive case study in why hardware “end-of-life” dates must be treated by organizations as a hard security deadline rather than a budgetary suggestion.